Opal44 vs Threat Watch
Side-by-side comparison to help you choose the right tool.
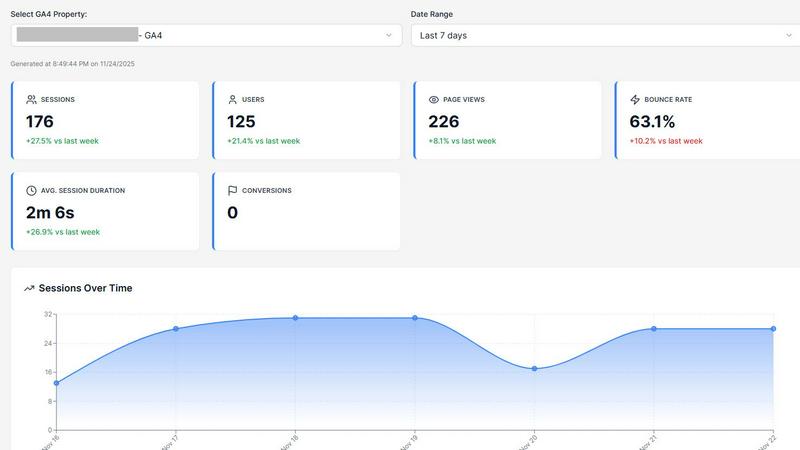
Opal44 delivers AI-driven insights from your website traffic in plain English, making analytics simple and actionable.
Last updated: March 4, 2026
Threat Watch
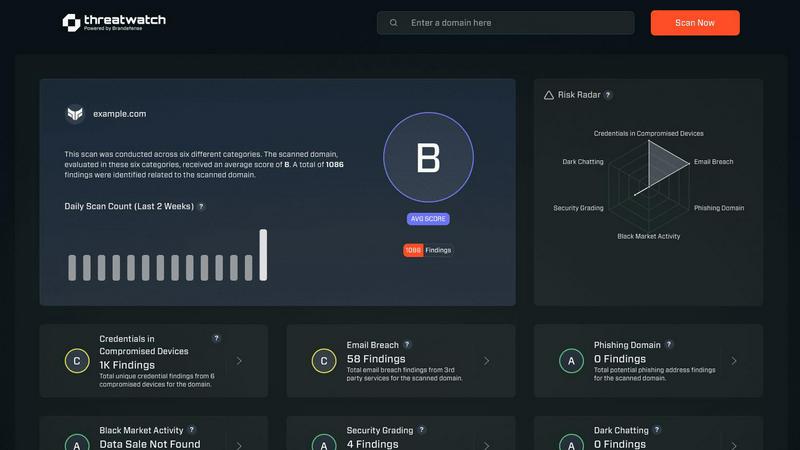
Secure your digital world with Threat Watch, instantly revealing compromised accounts and devices for essential.
Last updated: March 1, 2026
Visual Comparison
Opal44
Threat Watch
Feature Comparison
Opal44
Plain English Insights
Opal44's AI seamlessly connects to your Google Analytics 4 data, translating complex metrics into clear, everyday language. This feature allows users to grasp what's happening on their website without the need for technical jargon, making analytics accessible to everyone.
Conversation-Style Reports
With Opal44, analytics reports read like a friendly conversation with your own personal analytics guide. This feature ensures that you receive updates in a clear, engaging manner, making it easier for users of all backgrounds to understand and act on the insights provided.
Smart, Data-Driven Tips
Tailored recommendations are generated based on your specific GA4 data, helping you improve website traffic and overall performance. This feature equips users with actionable strategies to optimize their digital presence and make data-driven decisions effectively.
Real-Time Alerts
Stay informed about significant changes in your website traffic with Opal44's real-time alerts. This feature notifies you immediately of traffic spikes, drops, or unusual activity, allowing you to respond swiftly and effectively to fluctuations in your data.
Threat Watch
Comprehensive Asset Analysis
Threat Watch provides an in-depth analysis of all organizational assets, identifying potential vulnerabilities and exposures that could be exploited by cybercriminals. This feature ensures that businesses have a clear understanding of their security landscape.
Real-Time Threat Insights
With real-time insights, Threat Watch keeps organizations informed about emerging threats and vulnerabilities. This timely information allows businesses to act swiftly and effectively, minimizing the potential impact of cyber incidents.
Automated Risk Assessment
The automated risk assessment feature streamlines the evaluation of security threats, saving time and resources. By automatically identifying and prioritizing risks, organizations can focus on the most critical issues, enhancing their overall security strategy.
Dark Web Monitoring
Threat Watch includes dark web monitoring to detect compromised credentials and sensitive information that may be available for sale. This proactive feature enables organizations to take immediate action to protect their data and reduce the risk of identity theft and fraud.
Use Cases
Opal44
Enhancing Marketing Strategies
Marketers can use Opal44 to gain insights into website traffic patterns, enabling them to refine their campaigns based on actual data rather than assumptions. This leads to more effective marketing strategies and improved ROI.
Streamlining Client Reporting
Digital agencies can leverage Opal44 to present analytics to clients in a way that is easily digestible. By using plain language reports, agencies can foster better communication and understanding, leading to more productive strategy sessions.
Improving Conversion Rates
E-commerce managers can utilize Opal44's smart recommendations to identify areas for improvement on their websites. This insight helps in optimizing product pages and checkout processes, ultimately boosting conversion rates and sales.
Simplifying Data Interpretation for Non-Technical Users
Content creators and non-technical professionals can benefit from Opal44 by simplifying the often daunting task of analyzing website data. With clear insights, they can focus on creating content that resonates with their audience without getting bogged down by complex metrics.
Threat Watch
Proactive Threat Mitigation
Organizations can utilize Threat Watch to proactively identify and mitigate potential threats before they escalate into significant incidents. By employing its comprehensive analysis capabilities, businesses can enhance their security posture.
Compliance and Regulatory Adherence
Threat Watch helps organizations meet compliance and regulatory requirements by providing detailed insights into their cybersecurity health. This ensures that businesses remain aligned with industry standards and avoid potential penalties.
Incident Response Preparation
By leveraging the real-time insights and automated risk assessments of Threat Watch, organizations can better prepare for incident response. This feature ensures that teams are equipped with the necessary information to respond effectively to security breaches.
Employee Awareness and Training
Threat Watch can be used to educate employees about potential threats such as phishing addresses and compromised accounts. By raising awareness, organizations can foster a security-conscious culture and reduce the likelihood of human error leading to security breaches.
Overview
About Opal44
Opal44 is an innovative analytics tool that transforms complex website traffic data from Google Analytics 4 into accessible, actionable insights delivered in plain English. Designed for businesses of all sizes, from small startups to large organizations, Opal44 eliminates the confusion surrounding traditional analytics dashboards, making data interpretation straightforward and comprehensible. Its primary value proposition lies in its ability to provide real-time insights and recommendations that enable users to improve website performance without the need for technical expertise. With Opal44, you can ask simple questions about your website traffic and receive clear answers, helping you make informed decisions that drive growth. Whether you are a marketing professional, business owner, or content creator, Opal44 empowers you to understand your data and leverage it for better outcomes, all while ensuring your data remains secure and private.
About Threat Watch
Threat Watch is a state-of-the-art cybersecurity intelligence solution tailored to empower organizations with critical insights into their cyber health. It systematically analyzes an organization's assets, vulnerabilities, and exposures, providing a thorough overview of security status. Designed for businesses of all sizes, Threat Watch integrates real-time insights with automated assessments, allowing for the swift identification, prioritization, and mitigation of risks. By evaluating crucial security categories such as compromised credentials, breached accounts, phishing addresses, and dark web content, it equips users with essential information to take proactive measures against potential threats. The main value proposition lies in its ability to streamline the cybersecurity process, enabling organizations to respond more effectively to incidents and safeguard their digital assets. With Threat Watch, organizations can uncover their cybersecurity health quickly, ensuring they remain ahead of evolving threats.
Frequently Asked Questions
Opal44 FAQ
What is Opal44?
Opal44 is an AI-powered analytics tool that interprets Google Analytics 4 data and delivers insights in plain English, making it easy for users to understand their website traffic without technical jargon.
How does Opal44 ensure data privacy?
Opal44 prioritizes your data security by never selling or sharing your Google Analytics data. Your information remains exclusively yours, ensuring privacy and trust.
Can I try Opal44 for free?
Yes, new users can start with a 7-day free trial that allows for 50 actions without the need for a credit card. This gives you the opportunity to explore all features risk-free.
What kind of support does Opal44 offer?
Opal44 provides email support for all users, with priority support and onboarding available for Professional and Agency plan subscribers. This ensures you have the help you need whenever you need it.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for businesses of all sizes, from small startups to large enterprises. Its comprehensive features make it suitable for any organization looking to enhance its cybersecurity posture.
How does Threat Watch identify compromised credentials?
Threat Watch utilizes advanced scanning techniques to monitor various databases and dark web sources for compromised credentials associated with an organization's assets. This proactive monitoring helps organizations take immediate action.
Can Threat Watch integrate with existing security systems?
Yes, Threat Watch is designed to integrate seamlessly with existing cybersecurity tools and systems, enhancing an organization's overall security framework without disrupting current operations.
Is there a trial period available for Threat Watch?
Yes, Threat Watch offers a free scan for organizations to assess their cybersecurity health. This trial allows potential users to experience the solution's capabilities before committing to a subscription.
Alternatives
Opal44 Alternatives
Opal44 is an innovative tool that falls under the category of Business Intelligence, specifically designed to provide users with AI-powered insights into their website traffic through simple, actionable language. It harnesses the power of Google Analytics 4, translating complex data into easily understandable information without the use of technical jargon. This makes it an essential resource for businesses looking to optimize their online presence and enhance user engagement. Users often seek alternatives to Opal44 for a variety of reasons, including pricing structures, specific feature sets, or compatibility with different platforms. As businesses grow and their needs evolve, the search for tools that align better with their unique requirements becomes essential. When selecting an alternative, it is crucial to consider factors such as ease of use, the comprehensiveness of features, customer support, and how well the solution integrates with existing systems or workflows.
Threat Watch Alternatives
Threat Watch is a state-of-the-art cybersecurity intelligence solution designed to provide organizations with vital insights into their cybersecurity health. It falls under the business intelligence category, focusing on the assessment and management of security risks. Users often seek alternatives to Threat Watch for various reasons, including pricing concerns, feature sets that may better align with specific needs, or compatibility with existing platforms. When choosing an alternative, it’s essential to consider factors such as the comprehensiveness of security evaluations, the availability of real-time insights, and the effectiveness of automated assessments. The alternatives you explore should offer robust capabilities, particularly in monitoring compromised accounts and devices, as well as providing dark web insights. It's crucial to ensure that any replacement solution can deliver the same level of security assurance and operational efficiency that Threat Watch offers, thus enabling your organization to maintain a proactive stance against evolving cyber threats.