Threat Watch
Secure your digital world with Threat Watch, instantly revealing compromised accounts and devices for essential.
Visit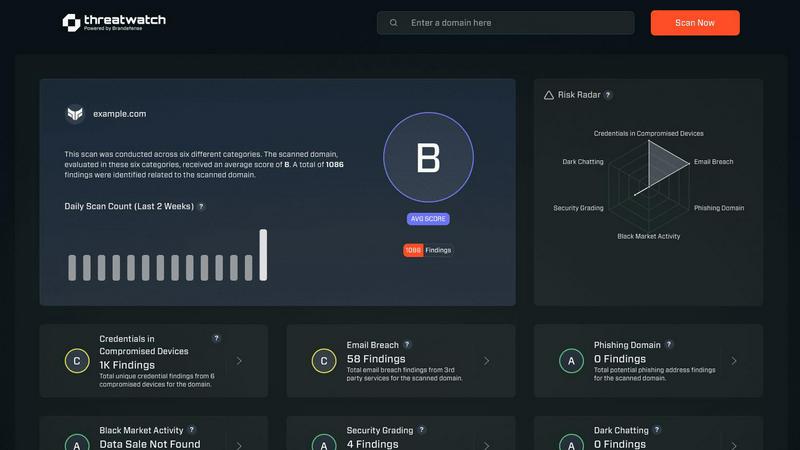
About Threat Watch
Threat Watch is a state-of-the-art cybersecurity intelligence solution tailored to empower organizations with critical insights into their cyber health. It systematically analyzes an organization's assets, vulnerabilities, and exposures, providing a thorough overview of security status. Designed for businesses of all sizes, Threat Watch integrates real-time insights with automated assessments, allowing for the swift identification, prioritization, and mitigation of risks. By evaluating crucial security categories such as compromised credentials, breached accounts, phishing addresses, and dark web content, it equips users with essential information to take proactive measures against potential threats. The main value proposition lies in its ability to streamline the cybersecurity process, enabling organizations to respond more effectively to incidents and safeguard their digital assets. With Threat Watch, organizations can uncover their cybersecurity health quickly, ensuring they remain ahead of evolving threats.
Features of Threat Watch
Comprehensive Asset Analysis
Threat Watch provides an in-depth analysis of all organizational assets, identifying potential vulnerabilities and exposures that could be exploited by cybercriminals. This feature ensures that businesses have a clear understanding of their security landscape.
Real-Time Threat Insights
With real-time insights, Threat Watch keeps organizations informed about emerging threats and vulnerabilities. This timely information allows businesses to act swiftly and effectively, minimizing the potential impact of cyber incidents.
Automated Risk Assessment
The automated risk assessment feature streamlines the evaluation of security threats, saving time and resources. By automatically identifying and prioritizing risks, organizations can focus on the most critical issues, enhancing their overall security strategy.
Dark Web Monitoring
Threat Watch includes dark web monitoring to detect compromised credentials and sensitive information that may be available for sale. This proactive feature enables organizations to take immediate action to protect their data and reduce the risk of identity theft and fraud.
Use Cases of Threat Watch
Proactive Threat Mitigation
Organizations can utilize Threat Watch to proactively identify and mitigate potential threats before they escalate into significant incidents. By employing its comprehensive analysis capabilities, businesses can enhance their security posture.
Compliance and Regulatory Adherence
Threat Watch helps organizations meet compliance and regulatory requirements by providing detailed insights into their cybersecurity health. This ensures that businesses remain aligned with industry standards and avoid potential penalties.
Incident Response Preparation
By leveraging the real-time insights and automated risk assessments of Threat Watch, organizations can better prepare for incident response. This feature ensures that teams are equipped with the necessary information to respond effectively to security breaches.
Employee Awareness and Training
Threat Watch can be used to educate employees about potential threats such as phishing addresses and compromised accounts. By raising awareness, organizations can foster a security-conscious culture and reduce the likelihood of human error leading to security breaches.
Frequently Asked Questions
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for businesses of all sizes, from small startups to large enterprises. Its comprehensive features make it suitable for any organization looking to enhance its cybersecurity posture.
How does Threat Watch identify compromised credentials?
Threat Watch utilizes advanced scanning techniques to monitor various databases and dark web sources for compromised credentials associated with an organization's assets. This proactive monitoring helps organizations take immediate action.
Can Threat Watch integrate with existing security systems?
Yes, Threat Watch is designed to integrate seamlessly with existing cybersecurity tools and systems, enhancing an organization's overall security framework without disrupting current operations.
Is there a trial period available for Threat Watch?
Yes, Threat Watch offers a free scan for organizations to assess their cybersecurity health. This trial allows potential users to experience the solution's capabilities before committing to a subscription.
Explore more in this category:
Similar to Threat Watch
FX Radar
FX Radar delivers real-time forex and financial news, empowering traders with instant insights and professional performance tracking tools.
AI Business Name Generator
Instantly generate unique and memorable business names with our essential AI Business Name Generator, perfect for startups and brands.
MarketWrk
MarketWrk automates CPG pricing and MAP monitoring to transform raw data into actionable insights, saving your team time and money.
Opal44
Opal44 delivers AI-driven insights from your website traffic in plain English, making analytics simple and actionable.
Fusedash
Fusedash transforms raw data into insightful dashboards and charts, empowering teams to act on insights instantly.
finban
finban empowers you to confidently plan liquidity for hiring, taxes, and investments without Excel chaos.
Zignt
Zignt is the essential tool for secure, instant contract signing with unlimited templates and no per-signature fees.
aVenture
aVenture is an essential AI platform for precise research on private companies, investors, and market trends.