iGPT vs Threat Watch
Side-by-side comparison to help you choose the right tool.
iGPT gives enterprise AI agents secure, auditable access to email intelligence and context.
Last updated: March 1, 2026
Threat Watch
Secure your digital world with Threat Watch, instantly revealing compromised accounts and devices for essential.
Last updated: March 1, 2026
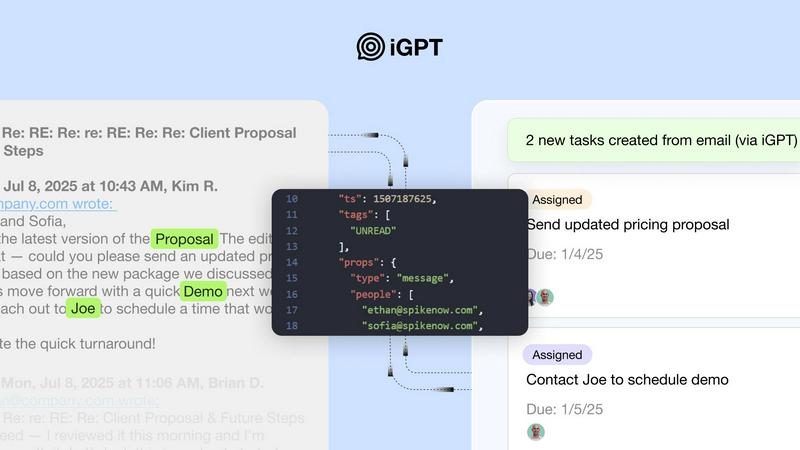
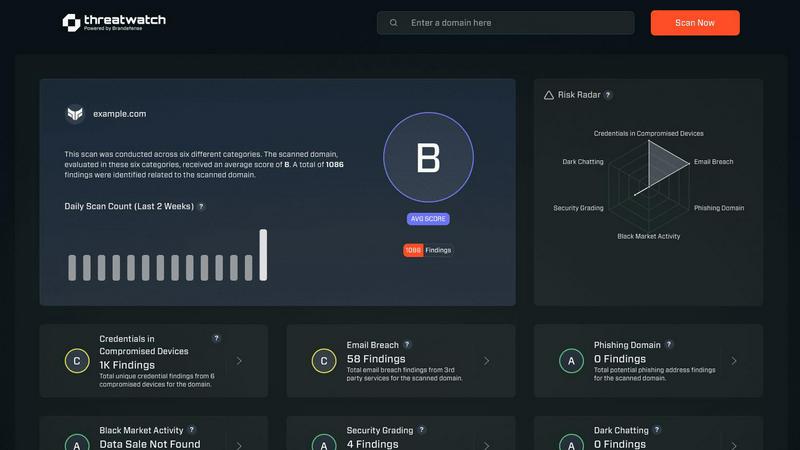
Visual Comparison
iGPT
Threat Watch
Feature Comparison
iGPT
Unified Natural Language Endpoint
Replace complex, multi-step retrieval pipelines with a single, powerful API call. There is no need to manage separate systems for parsing, vector storage, or prompt chaining. You simply send a natural language query, and iGPT's integrated pipeline handles retrieval, context shaping, and reasoning automatically, returning ready-to-use answers in approximately 200ms for retrieval and ~3s to first token.
Deep Communication Indexing & Thread Reconstruction
iGPT does the hard work of making sense of your communication data. It automatically and deeply indexes emails and all attachment data in real-time. Crucially, it reconstructs fragmented email threads across time, participants, and attachments, rebuilding the complete conversation context that is essential for accurate understanding and actionable intelligence.
Context Engineering Framework (CEF)
This proprietary system optimizes context windows for your LLM automatically, eliminating the need for manual prompt tuning. It employs hybrid retrieval (semantic + keyword + filters), scores and reranks results in one call, and shapes the optimal context to deliver precise, cited answers that link directly back to source messages and documents.
Enterprise-Grade Security & Compliance
Security is not an add-on; it's foundational. iGPT enforces strict OAuth-only processing with Role-Based Access Control (RBAC) for every request. It maintains a full audit trail and adheres to a strict zero data retention policy, processing inferences only in memory. Most importantly, your data is never used to train or improve any models.
Threat Watch
Comprehensive Asset Analysis
Threat Watch provides an in-depth analysis of all organizational assets, identifying potential vulnerabilities and exposures that could be exploited by cybercriminals. This feature ensures that businesses have a clear understanding of their security landscape.
Real-Time Threat Insights
With real-time insights, Threat Watch keeps organizations informed about emerging threats and vulnerabilities. This timely information allows businesses to act swiftly and effectively, minimizing the potential impact of cyber incidents.
Automated Risk Assessment
The automated risk assessment feature streamlines the evaluation of security threats, saving time and resources. By automatically identifying and prioritizing risks, organizations can focus on the most critical issues, enhancing their overall security strategy.
Dark Web Monitoring
Threat Watch includes dark web monitoring to detect compromised credentials and sensitive information that may be available for sale. This proactive feature enables organizations to take immediate action to protect their data and reduce the risk of identity theft and fraud.
Use Cases
iGPT
AI-Powered Email Assistants & Copilots
Build intelligent agents that can draft, prioritize, summarize, and act on email with full historical and contextual understanding. These assistants can manage inboxes, flag urgent items, and automate follow-ups by comprehending the entire thread and attached documents, not just the latest message.
Automated Workflow & CRM Enrichment
Automatically turn email conversations into structured actions. Extract decisions, owners, deadlines, and deal momentum directly from sales and support threads to update CRM systems, create tasks in project tools, and flag stalled processes, ensuring no critical action item falls through the cracks.
Customer Support & Success Copilots
Empower support teams with agents that instantly rebuild the complete customer story. By analyzing long email chains, attachments, and subtle tone shifts, these copilots provide agents with immediate context, suggested responses, and summarized histories, drastically reducing resolution time and improving customer experience.
Compliance Auditing & Document Intelligence
Automate the traceability of feedback, approvals, and business rationale directly back to the original email conversations and attached files. Extract and summarize key information from contracts, invoices, and reports within the context of the surrounding discussion for audit trails and compliance reporting.
Threat Watch
Proactive Threat Mitigation
Organizations can utilize Threat Watch to proactively identify and mitigate potential threats before they escalate into significant incidents. By employing its comprehensive analysis capabilities, businesses can enhance their security posture.
Compliance and Regulatory Adherence
Threat Watch helps organizations meet compliance and regulatory requirements by providing detailed insights into their cybersecurity health. This ensures that businesses remain aligned with industry standards and avoid potential penalties.
Incident Response Preparation
By leveraging the real-time insights and automated risk assessments of Threat Watch, organizations can better prepare for incident response. This feature ensures that teams are equipped with the necessary information to respond effectively to security breaches.
Employee Awareness and Training
Threat Watch can be used to educate employees about potential threats such as phishing addresses and compromised accounts. By raising awareness, organizations can foster a security-conscious culture and reduce the likelihood of human error leading to security breaches.
Overview
About iGPT
iGPT is the essential enterprise-grade API that transforms the unstructured chaos of email and communication data into actionable, context-aware intelligence for AI agents and workflows. It solves the critical, pervasive problem where most AI systems fail: understanding the complex, messy reality of email threads, attachments, and ongoing conversations where real business decisions and work actually happen. Built for developers and enterprises, iGPT delivers a secure, auditable gateway that deeply indexes all communication data, providing a unified natural language interface. Its core, non-negotiable value proposition is eliminating the immense and ongoing engineering burden of parsing, chunking, indexing, and endless prompt tuning. With a single API call, teams can instantly retrieve precise answers, extract structured data, and automate follow-ups, all with full citations to source emails and documents. This enables organizations to confidently and finally deploy powerful agentic systems for sales, customer success, operations, and compliance, knowing their sensitive data is processed with end-to-end security, granular access controls, and strict zero data retention policies.
About Threat Watch
Threat Watch is a state-of-the-art cybersecurity intelligence solution tailored to empower organizations with critical insights into their cyber health. It systematically analyzes an organization's assets, vulnerabilities, and exposures, providing a thorough overview of security status. Designed for businesses of all sizes, Threat Watch integrates real-time insights with automated assessments, allowing for the swift identification, prioritization, and mitigation of risks. By evaluating crucial security categories such as compromised credentials, breached accounts, phishing addresses, and dark web content, it equips users with essential information to take proactive measures against potential threats. The main value proposition lies in its ability to streamline the cybersecurity process, enabling organizations to respond more effectively to incidents and safeguard their digital assets. With Threat Watch, organizations can uncover their cybersecurity health quickly, ensuring they remain ahead of evolving threats.
Frequently Asked Questions
iGPT FAQ
How does iGPT handle data privacy and security?
iGPT is built with enterprise-grade security as a core principle. It employs OAuth-only authentication with strict Role-Based Access Control (RBAC). It operates on a zero data retention policy, meaning all inputs, prompts, and outputs are processed in memory and never stored. Furthermore, your data is absolutely never used to train or improve any AI models.
What types of email sources and attachments can iGPT connect to?
iGPT is designed to connect to and deeply index data from major enterprise email providers and protocols. It automatically processes and extracts text, data, and structure from a wide array of attachments including documents, PDFs, spreadsheets, and presentations, making the content within them searchable and actionable.
Do I need to manage vector databases or complex prompt chains?
No. This is the primary burden iGPT eliminates. There is no need for you to parse text, chunk documents, manage vector stores, or continuously tune prompts. You connect your data sources and make natural language queries to the unified API endpoint. iGPT handles the entire complex context engineering pipeline for you.
How does iGPT ensure the answers are accurate and trustworthy?
iGPT provides fully cited answers for every response. Each piece of information or conclusion generated by the system is directly linked back to the source email messages and specific attachments it was derived from. This creates an audit trail and allows users to verify the accuracy and context of the information provided.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for businesses of all sizes, from small startups to large enterprises. Its comprehensive features make it suitable for any organization looking to enhance its cybersecurity posture.
How does Threat Watch identify compromised credentials?
Threat Watch utilizes advanced scanning techniques to monitor various databases and dark web sources for compromised credentials associated with an organization's assets. This proactive monitoring helps organizations take immediate action.
Can Threat Watch integrate with existing security systems?
Yes, Threat Watch is designed to integrate seamlessly with existing cybersecurity tools and systems, enhancing an organization's overall security framework without disrupting current operations.
Is there a trial period available for Threat Watch?
Yes, Threat Watch offers a free scan for organizations to assess their cybersecurity health. This trial allows potential users to experience the solution's capabilities before committing to a subscription.
Alternatives
iGPT Alternatives
iGPT is an enterprise-grade API that transforms unstructured email and communication data into actionable intelligence for AI agents. It belongs to the business intelligence category, specifically solving the complex problem of giving AI secure, auditable context from messy email threads and attachments. Users often explore alternatives for various reasons, including budget constraints, specific feature requirements, or the need to integrate with a different technical stack or platform. The search for a different solution is a common step in evaluating the right tool for a project's unique demands. When considering an alternative, prioritize solutions that directly address the core challenge: securely turning communication chaos into reliable, context-aware intelligence. Essential evaluation criteria include the depth of email and attachment indexing, the robustness of security and access controls, and the overall engineering effort required to deploy and maintain the system.
Threat Watch Alternatives
Threat Watch is a state-of-the-art cybersecurity intelligence solution designed to provide organizations with vital insights into their cybersecurity health. It falls under the business intelligence category, focusing on the assessment and management of security risks. Users often seek alternatives to Threat Watch for various reasons, including pricing concerns, feature sets that may better align with specific needs, or compatibility with existing platforms. When choosing an alternative, it’s essential to consider factors such as the comprehensiveness of security evaluations, the availability of real-time insights, and the effectiveness of automated assessments. The alternatives you explore should offer robust capabilities, particularly in monitoring compromised accounts and devices, as well as providing dark web insights. It's crucial to ensure that any replacement solution can deliver the same level of security assurance and operational efficiency that Threat Watch offers, thus enabling your organization to maintain a proactive stance against evolving cyber threats.