Pursuit vs Threat Watch
Side-by-side comparison to help you choose the right tool.
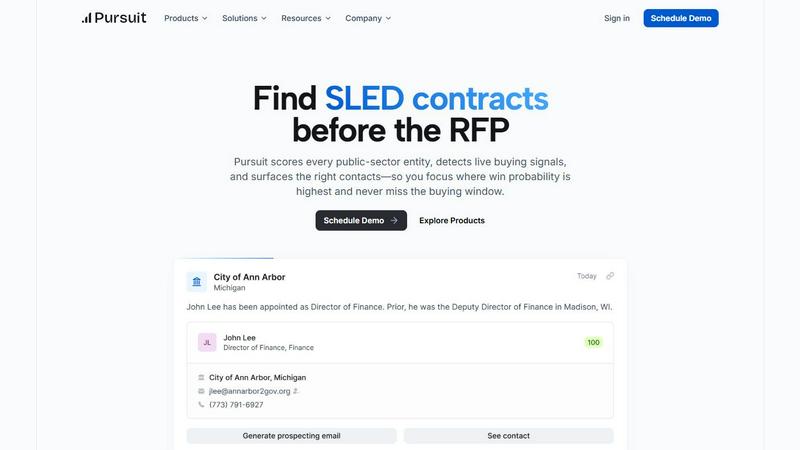
Pursuit
Pursuit finds and scores public sector contracts so you win more deals.
Last updated: February 28, 2026
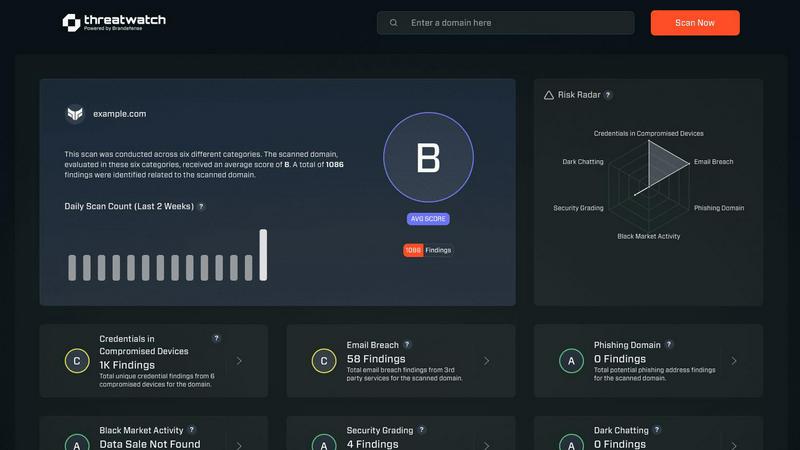
Threat Watch
Secure your digital world with Threat Watch, instantly revealing compromised accounts and devices for essential.
Last updated: March 1, 2026
Visual Comparison
Pursuit
Threat Watch
Feature Comparison
Pursuit
Pre-RFP Signal Detection
Pursuit's core engine continuously monitors and analyzes millions of data points from council meetings, budget documents, and procurement portals to detect genuine buying intent 6-18 months before an RFP is released. This critical early warning system identifies budget approvals, strategic initiatives, and contract expirations, allowing your team to engage during the formative stage of a procurement, long before public bidding begins.
Entity Scoring & Prioritization
The platform automatically scores and ranks all 110,000+ SLED entities based on live buying signals, budget cycles, and your specific solution fit. This eliminates wasted time on low-probability targets and provides daily, prioritized lists for sales development reps and account executives, ensuring every outreach effort is directed at agencies with the highest imminent need and likelihood to purchase.
Automated Contact & Account Enrichment
Pursuit maintains a constantly updated database of public sector contacts, complete with accurate direct dials, email addresses, and organizational charts. With 94% data accuracy and native bi-directional sync with Salesforce and HubSpot, it eliminates manual data entry and enrichment, ensuring your CRM reflects the true, current state of your target accounts without any engineering effort.
Integrated Chrome Extension for Meeting Intelligence
Sales and customer success teams gain instant, in-context intelligence for every interaction. The Chrome extension provides a complete dossier on any entity directly in your browser, including known incumbents, contract values, procurement history, and recent buying signals, enabling perfectly prepared and relevant conversations that improve win rates by over 30%.
Threat Watch
Comprehensive Asset Analysis
Threat Watch provides an in-depth analysis of all organizational assets, identifying potential vulnerabilities and exposures that could be exploited by cybercriminals. This feature ensures that businesses have a clear understanding of their security landscape.
Real-Time Threat Insights
With real-time insights, Threat Watch keeps organizations informed about emerging threats and vulnerabilities. This timely information allows businesses to act swiftly and effectively, minimizing the potential impact of cyber incidents.
Automated Risk Assessment
The automated risk assessment feature streamlines the evaluation of security threats, saving time and resources. By automatically identifying and prioritizing risks, organizations can focus on the most critical issues, enhancing their overall security strategy.
Dark Web Monitoring
Threat Watch includes dark web monitoring to detect compromised credentials and sensitive information that may be available for sale. This proactive feature enables organizations to take immediate action to protect their data and reduce the risk of identity theft and fraud.
Use Cases
Pursuit
For Sales Leaders: Building a Predictable Pipeline
Sales executives use Pursuit to gain complete visibility into team activity and pipeline health based on real SLED buying indicators. They can identify coverage gaps, forecast with confidence using early-stage signal data, and strategically allocate resources. This intelligence-driven approach has proven to increase pipeline by 6.6x without adding new headcount, transforming SLED sales from a reactive gamble into a predictable engine.
For BDRs/SDRs: Prioritized, High-Impact Outreach
Business Development Representatives stop cold calling blindly. Pursuit delivers daily, territory-specific call lists based on live signals like recent budget approvals or leadership changes. This ensures every call and email is timely and relevant, directly contributing to a documented 47% increase in qualified pipeline and a 20% cold call conversion rate by engaging buyers when they are actively seeking solutions.
For Marketing: Signal-Driven ABM Campaigns
Marketing teams build highly effective Account-Based Marketing campaigns around actual buying signals instead of firmographics. By syncing audiences of in-market accounts to platforms like LinkedIn, Marketo, or HubSpot, they can deliver targeted content about budget cycles and new initiatives, resulting in a 2.4x lift in campaign conversion rates by aligning marketing efforts directly with the procurement calendar.
For Customer Success: Proactive Renewal & Expansion
Customer Success Managers configure alerts for key events 90-180 days before contract renewals. They also monitor accounts for churn signals like budget cuts or competitor interest. This early intelligence allows for proactive renewal conversations and identifying expansion opportunities, leading to a 3x faster renewal identification process and significantly reducing customer attrition risk.
Threat Watch
Proactive Threat Mitigation
Organizations can utilize Threat Watch to proactively identify and mitigate potential threats before they escalate into significant incidents. By employing its comprehensive analysis capabilities, businesses can enhance their security posture.
Compliance and Regulatory Adherence
Threat Watch helps organizations meet compliance and regulatory requirements by providing detailed insights into their cybersecurity health. This ensures that businesses remain aligned with industry standards and avoid potential penalties.
Incident Response Preparation
By leveraging the real-time insights and automated risk assessments of Threat Watch, organizations can better prepare for incident response. This feature ensures that teams are equipped with the necessary information to respond effectively to security breaches.
Employee Awareness and Training
Threat Watch can be used to educate employees about potential threats such as phishing addresses and compromised accounts. By raising awareness, organizations can foster a security-conscious culture and reduce the likelihood of human error leading to security breaches.
Overview
About Pursuit
Pursuit is the essential, non-negotiable intelligence platform for any business selling to the state, local, and education (SLED) government market. This $2 trillion sector is notoriously difficult to penetrate, characterized by over 110,000 unique entities, labyrinthine procurement rules, and buying cycles that span fiscal years. Traditional sales methods—relying on manual research and fragile personal networks—are a recipe for missed opportunities and inefficient spending. Pursuit solves this fundamental problem by replacing guesswork with automated, actionable intelligence. It is a necessary operational system designed exclusively for government contractors, technology vendors, and professional service firms. The platform's indispensable mission is to surface critical buying signals 6-18 months before an RFP is formally issued, transforming your team from an outsider to the perceived incumbent. By scoring every public-sector entity, detecting live signals from documents and meetings, and surfacing exact contacts, Pursuit ensures your sales efforts are focused exclusively where the win probability is highest. For building a predictable and dominant SLED pipeline, Pursuit is not a luxury; it is the required foundation for modern public sector sales success.
About Threat Watch
Threat Watch is a state-of-the-art cybersecurity intelligence solution tailored to empower organizations with critical insights into their cyber health. It systematically analyzes an organization's assets, vulnerabilities, and exposures, providing a thorough overview of security status. Designed for businesses of all sizes, Threat Watch integrates real-time insights with automated assessments, allowing for the swift identification, prioritization, and mitigation of risks. By evaluating crucial security categories such as compromised credentials, breached accounts, phishing addresses, and dark web content, it equips users with essential information to take proactive measures against potential threats. The main value proposition lies in its ability to streamline the cybersecurity process, enabling organizations to respond more effectively to incidents and safeguard their digital assets. With Threat Watch, organizations can uncover their cybersecurity health quickly, ensuring they remain ahead of evolving threats.
Frequently Asked Questions
Pursuit FAQ
What makes SLED sales different from commercial sales?
SLED sales are governed by public procurement laws, involve extremely long budget cycles (often 12-24 months), and require navigating a vast, fragmented landscape of over 110,000 independent entities each with its own rules. Success depends on timing your engagement to align with these rigid budget and planning cycles, not just having a good product or relationship. Missing a key budget window can mean waiting an entire fiscal year for the next opportunity.
How does Pursuit find buying signals before the RFP?
Pursuit's AI-powered platform scans and analyzes millions of unstructured public documents that indicate future intent, including city council meeting minutes, approved budget documents, strategic planning sessions, and board of education notes. It identifies discussions about new initiatives, technology needs, and contract expirations, translating them into actionable, scored signals long before a formal procurement document is ever drafted.
Can Pursuit integrate with our existing tech stack (CRM, etc.)?
Absolutely. Pursuit is built for seamless integration. It offers native, bi-directional synchronization with major CRMs like Salesforce and HubSpot, ensuring all account scores, contact details, and buying signals flow automatically into your systems of record. It also pushes audience lists directly to marketing platforms like Marketo and LinkedIn Campaign Manager, requiring no engineering resources to maintain.
Is Pursuit suitable for companies new to the SLED market?
Yes, Pursuit is arguably even more critical for newcomers. It provides the necessary infrastructure to understand and navigate the complex SLED landscape efficiently from day one. Instead of spending months on manual, ineffective research, new market entrants can immediately identify the highest-probability targets and engage with perfect timing, accelerating their time-to-revenue and avoiding costly missteps.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for businesses of all sizes, from small startups to large enterprises. Its comprehensive features make it suitable for any organization looking to enhance its cybersecurity posture.
How does Threat Watch identify compromised credentials?
Threat Watch utilizes advanced scanning techniques to monitor various databases and dark web sources for compromised credentials associated with an organization's assets. This proactive monitoring helps organizations take immediate action.
Can Threat Watch integrate with existing security systems?
Yes, Threat Watch is designed to integrate seamlessly with existing cybersecurity tools and systems, enhancing an organization's overall security framework without disrupting current operations.
Is there a trial period available for Threat Watch?
Yes, Threat Watch offers a free scan for organizations to assess their cybersecurity health. This trial allows potential users to experience the solution's capabilities before committing to a subscription.
Alternatives
Pursuit Alternatives
Pursuit is an AI-powered business intelligence platform designed to help companies win public sector contracts. It automates the search for SLED government opportunities, providing early buying signals and key contact data to build a predictable sales pipeline. Users may explore alternatives for several reasons, including budget constraints, specific feature requirements, or the need for a different platform integration. The search often stems from a need to solve the core problem of inefficient, manual public sector sales research with a tool that fits their operational scale. When evaluating any alternative, focus on its ability to automate opportunity discovery, provide accurate and timely data on SLED entities, and deliver actionable intelligence that directly translates to higher win rates. The essential criteria are coverage, data freshness, and the platform's capacity to identify opportunities long before an RFP is issued.
Threat Watch Alternatives
Threat Watch is a state-of-the-art cybersecurity intelligence solution designed to provide organizations with vital insights into their cybersecurity health. It falls under the business intelligence category, focusing on the assessment and management of security risks. Users often seek alternatives to Threat Watch for various reasons, including pricing concerns, feature sets that may better align with specific needs, or compatibility with existing platforms. When choosing an alternative, it’s essential to consider factors such as the comprehensiveness of security evaluations, the availability of real-time insights, and the effectiveness of automated assessments. The alternatives you explore should offer robust capabilities, particularly in monitoring compromised accounts and devices, as well as providing dark web insights. It's crucial to ensure that any replacement solution can deliver the same level of security assurance and operational efficiency that Threat Watch offers, thus enabling your organization to maintain a proactive stance against evolving cyber threats.
