Perkoon vs Phishly
Side-by-side comparison to help you choose the right tool.
Perkoon enables free, unlimited peer-to-peer file transfers without signup, ensuring your files stay private and secure.
Last updated: March 4, 2026
Phishly
Phishly instantly detects phishing emails with AI to protect your inbox.
Visual Comparison
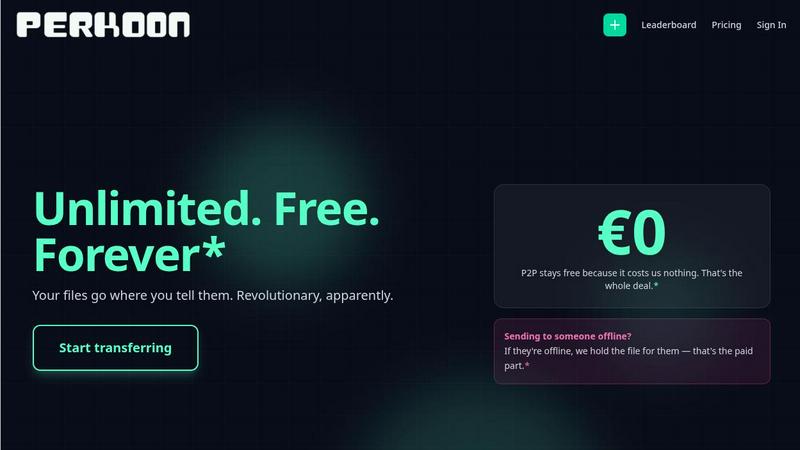
Perkoon
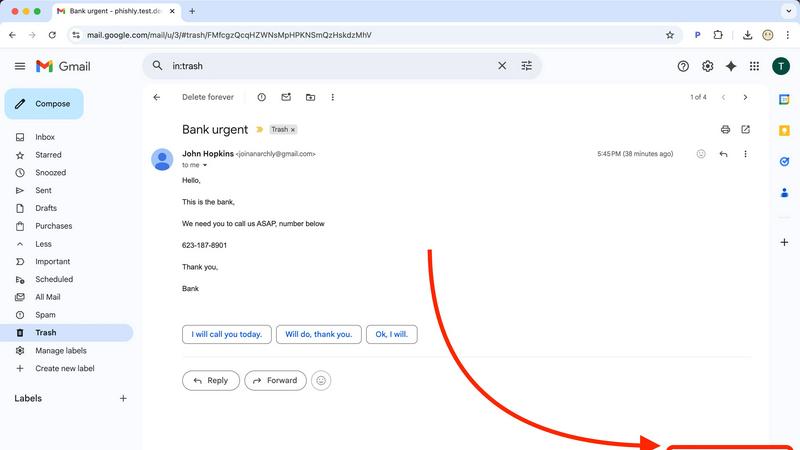
Phishly
Feature Comparison
Perkoon
Peer-to-Peer File Transfer
Perkoon’s flagship feature allows users to transfer files directly between browsers with no size limits and without creating accounts. This P2P method ensures that data privacy is maintained, as files do not pass through a central server, making file sharing seamless and secure.
Encrypted Cloud Storage
When sending files to offline recipients, Perkoon provides an encrypted cloud storage option. This feature is essential for securing your data while it is temporarily held until the recipient can access it, ensuring that privacy and security are never compromised.
Built-in Automation Tools
Designed for the modern user, Perkoon includes native automation tools that enable AI agents to interact with the service directly. This eliminates the need for screen-scraping and enhances the efficiency of file transfers, making it a powerful tool for tech-savvy users.
User-Friendly CLI Tool
Perkoon offers a simple command-line interface (CLI) tool that allows advanced users and developers to interact with the service effortlessly. This feature is perfect for those who prefer a more technical approach to file transfers, enhancing customization and control over the transfer process.
Phishly
One-Click Gmail Integration
Phishly integrates directly into your Gmail workflow as a lightweight Chrome extension, eliminating any complex setup or separate applications. When you encounter a questionable email, you don't need to forward it or copy text elsewhere. Simply open the email and click the "Scan with Phishly" button that appears. The analysis happens instantly within your inbox, providing a seamless and immediate security check without disrupting your productivity. This frictionless integration ensures you actually use the protection when you need it most.
AI-Powered Multi-Indicator Analysis
The core of Phishly is its sophisticated artificial intelligence engine, trained to identify a comprehensive range of phishing tactics. It doesn't just check links; it performs a deep analysis of the entire email content and headers. This includes detecting subtle signs like domain spoofing (where a sender address mimics a legitimate one), analyzing the emotional pressure of the language used, identifying mismatched URLs, and flagging requests for sensitive information. This multi-layered approach catches sophisticated attacks that simpler tools miss.
Clear, Actionable Risk Assessment
Phishly cuts through the noise and provides a definitive, easy-to-understand verdict. After analysis, it categorizes the email into one of three clear risk levels: Safe, Medium Risk, or High Risk. More importantly, it doesn't just give a score; it provides a detailed breakdown explaining why it reached that conclusion, listing each specific suspicious element found. This transparency educates the user, builds trust in the tool, and provides the context needed to make an informed decision about how to handle the email.
Privacy-First, On-Demand Scanning
Your email privacy is paramount. Unlike some security tools that scan all incoming mail automatically, Phishly operates on a strict, user-controlled, on-demand model. It only analyzes the content of emails you explicitly choose to scan by clicking the button or pasting text. The AI processes this data to provide the risk assessment, and there is no permanent storage or mining of your personal email content. This approach ensures powerful protection without compromising your confidential communications.
Use Cases
Perkoon
Everyday File Sharing
Perkoon is ideal for everyday users who need to send files quickly to friends or colleagues without the hassle of signing up for accounts. Whether it’s sharing vacation photos or work documents, Perkoon simplifies the process.
Large File Transfers
For professionals working with large files, such as designers or videographers, Perkoon’s P2P service allows for the transfer of hefty files without worries about size restrictions or costs, making it a reliable choice for creative industries.
Secure Business Communications
Businesses can utilize Perkoon for secure file transfers, ensuring that sensitive documents are sent privately and efficiently. The encrypted cloud storage feature provides an extra layer of security for important data.
Integration with AI Systems
Developers can leverage Perkoon’s built-in automation tools to integrate file transfer capabilities directly into their AI systems. This allows for streamlined workflows and enhances the productivity of AI-driven applications.
Phishly
Verifying Urgent Financial or Invoice Requests
You receive an email from what appears to be your bank, a vendor, or a service like PayPal claiming there is an urgent issue with your account or an invoice that must be paid immediately. These high-pressure tactics are classic phishing. Instead of panicking or clicking, you use Phishly to scan the email. The AI will check the sender's actual domain against the official one, analyze the language for urgency triggers, and inspect any links. The clear "High Risk" rating and explanation give you the confidence to delete the email and contact the institution directly through verified channels.
Screening Job Offer or Opportunity Scams
Job seekers are prime targets for phishing scams disguised as lucrative offers or interview requests. These emails often contain links to fake application portals or requests to download malware-laden documents. Before engaging with any unsolicited opportunity, scan the email with Phishly. It will detect signs of spoofed company domains, generic greetings, and suspicious attachment or link patterns. This allows you to avoid identity theft schemes and malware while safely pursuing legitimate opportunities.
Protecting Small Business Teams from Breaches
Small businesses often lack dedicated IT security staff, making them vulnerable targets. A single employee clicking a phishing link can compromise the entire company's network. By providing the Phishly Chrome extension to your team, you empower every employee to be the first line of defense. When anyone receives a suspicious email—whether it mimics a client, a shipping service, or an internal system alert—they can instantly scan it. This creates a culture of security and prevents costly data breaches without complex IT management.
Analyzing Forwarded Suspicious Messages
Friends, family, or less tech-savvy colleagues often forward emails asking, "Is this real?" Instead of relying on your gut feeling, you can use Phishly's web tool. Simply copy the full text and headers of the forwarded suspicious email and paste it into the Phishly website for an instant, objective analysis. This provides a reliable second opinion, helping you protect your loved ones and coworkers from scams with authoritative, AI-driven evidence.
Overview
About Perkoon
Perkoon is a revolutionary file transfer service designed to simplify your digital life by providing a straightforward way to move files from one point to another without unnecessary complications. It is tailored for individuals and businesses alike who are weary of cumbersome restrictions, obligatory sign-ups, and services that commoditize personal data. At the heart of Perkoon are two fundamental methods for file transfer: a free peer-to-peer (P2P) system that enables users to send files directly between browsers in real time, and a secure cloud storage option for offline transfers. The P2P feature ensures that there are no size limitations and no need for accounts, making it a hassle-free experience. Your data remains private, as it never touches a central server, allowing Perkoon to operate at no cost to users. For offline recipients, the paid cloud storage service provides necessary encryption to keep your files secure. Perkoon is uniquely positioned for the AI age, featuring built-in automation tools and a simple command-line interface, making it an ideal solution for both everyday users and AI systems.
About Phishly
In today's digital landscape, a single deceptive email can lead to devastating financial loss, data breaches, and identity theft. Phishing attacks are not a possibility; they are a constant, sophisticated threat targeting everyone. You need a vigilant, intelligent guard that operates precisely when your suspicion is triggered. Phishly is that essential shield. It is an AI-powered phishing detection platform designed to deliver instant, clear verdicts on suspicious emails. Available as a seamless Chrome extension for Gmail and a straightforward web tool, Phishly empowers you to take control of your inbox security. Simply open any email in Gmail and click "Scan with Phishly," or paste suspicious email content directly on the website for an immediate, in-depth analysis. The advanced AI meticulously scans for critical phishing indicators like suspicious sender domains, urgent or threatening language, spoofed identities, and complex social engineering tactics. It then provides a straightforward, actionable risk assessment: Safe, Medium Risk, or High Risk, accompanied by a detailed explanation of the red flags it found. Built for individuals, remote workers, and small businesses, Phishly offers enterprise-grade detection without the complexity or cost. Crucially, it respects your privacy by only analyzing emails you explicitly choose to scan. With no technical knowledge required and a free-to-use model, Phishly is the non-negotiable tool you need to stop guessing and start knowing what's in your inbox.
Frequently Asked Questions
Perkoon FAQ
Why is Perkoon free?
Perkoon operates its P2P transfer service free of charge because it incurs minimal costs. The cloud storage option, which is a paid feature, covers the necessary expenses for server maintenance, ensuring users can enjoy free transfers without hidden fees.
Can I transfer files if the recipient is offline?
Yes, Perkoon holds files for offline recipients using its encrypted cloud storage service. This allows users to send files even when the recipient is not currently available, ensuring that file transfers are convenient and flexible.
What browsers are compatible with Perkoon?
Perkoon works seamlessly with Chrome, Edge, and Brave browsers, which support unlimited file transfers. However, users of Firefox and Safari may experience certain restrictions due to browser limitations, so using a compatible browser is recommended for the best experience.
How does Perkoon ensure my privacy?
Perkoon prioritizes user privacy by employing a P2P model where files do not pass through central servers. In addition, the cloud storage service encrypts files, ensuring that even the company cannot see the contents of your transfers. Your data remains yours at all times.
Phishly FAQ
How does Phishly protect my privacy?
Phishly is built with a strict privacy-first principle. The tool only analyzes emails that you explicitly and manually choose to scan by clicking the "Scan with Phishly" button in Gmail or pasting content into the web tool. It does not automatically scan, read, or store your emails in the background. The analysis is performed to generate the risk report, and we do not mine, sell, or retain your personal email data. Your inbox remains confidential.
Is technical knowledge required to use Phishly?
Absolutely not. Phishly is designed for complete simplicity and requires zero technical expertise. Installing the Chrome extension is a standard one-click process from the Chrome Web Store. Once installed, using it is as simple as opening an email and clicking a single button. The results are presented in plain language with clear "Safe," "Medium Risk," or "High Risk" labels and straightforward explanations, making it accessible to everyone.
What makes Phishly different from my email provider's spam filter?
Your email provider's spam filter is a broad, automated layer that catches obvious spam but often misses sophisticated, targeted phishing emails (spear phishing). Phishly acts as your personal, on-demand forensic analyst. It uses advanced AI to examine the specific content, sender details, and psychological tactics of an email that has already passed through the basic spam filter, providing a second, much deeper layer of defense precisely when you are unsure.
Is Phishly really free to use?
Yes, the core phishing detection functionality of Phishly is completely free to use. You can install the Chrome extension and use the web analysis tool without any cost or subscription. This allows individuals and small businesses to access powerful AI-driven security protection without any financial barrier, making essential digital safety accessible to all.