Karolium vs Threat Watch
Side-by-side comparison to help you choose the right tool.
Karolium is a zero-code platform that empowers enterprises to rapidly create AI-driven business solutions and enhance.
Last updated: February 28, 2026
Threat Watch
Secure your digital world with Threat Watch, instantly revealing compromised accounts and devices for essential.
Last updated: March 1, 2026
Visual Comparison
Karolium

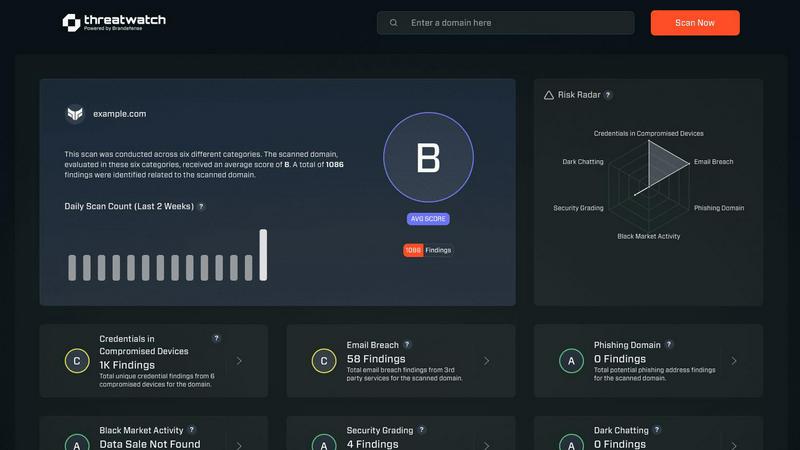
Threat Watch
Feature Comparison
Karolium
Zero-Code Development
Karolium's zero-code functionality allows users to create applications without any programming knowledge. This democratizes development, enabling teams across an organization to build and customize solutions that meet specific business needs.
Predictive and Prescriptive Analytics
The platform incorporates advanced analytics capabilities that empower organizations to forecast future trends and suggest actionable insights. This feature enhances strategic planning and supports data-driven decision-making.
Seamless Integration
Karolium ensures that new applications can be easily integrated into existing systems, whether they are legacy platforms or modern microservices. This eliminates the hassle of complex integration processes and accelerates deployment.
Pre-Composed Modules
With a library of ready-to-use, pre-composed modules, organizations can quickly assemble solutions tailored to their workflows. These modules enhance productivity by reducing the time and effort needed to develop applications from scratch.
Threat Watch
Comprehensive Asset Analysis
Threat Watch provides an in-depth analysis of all organizational assets, identifying potential vulnerabilities and exposures that could be exploited by cybercriminals. This feature ensures that businesses have a clear understanding of their security landscape.
Real-Time Threat Insights
With real-time insights, Threat Watch keeps organizations informed about emerging threats and vulnerabilities. This timely information allows businesses to act swiftly and effectively, minimizing the potential impact of cyber incidents.
Automated Risk Assessment
The automated risk assessment feature streamlines the evaluation of security threats, saving time and resources. By automatically identifying and prioritizing risks, organizations can focus on the most critical issues, enhancing their overall security strategy.
Dark Web Monitoring
Threat Watch includes dark web monitoring to detect compromised credentials and sensitive information that may be available for sale. This proactive feature enables organizations to take immediate action to protect their data and reduce the risk of identity theft and fraud.
Use Cases
Karolium
Accelerating Digital Transformation
Karolium serves as a catalyst for businesses looking to accelerate their digital transformation initiatives. By enabling rapid application development, organizations can respond quickly to changing market conditions and customer demands.
Enhancing Collaboration in Supply Chains
The platform allows businesses to improve supplier collaboration and centralize procurement processes. This helps streamline operations, reduce costs, and enhance overall supply chain efficiency.
Intelligent Decision-Making
Karolium empowers enterprises to make informed decisions by leveraging AI-driven insights. By predicting trends and recommending actions, organizations can enhance their strategic operations and achieve better outcomes.
Customizing Workflows
Organizations can utilize Karolium to create tailored workflows that align perfectly with their unique processes. This flexibility helps businesses overcome the limitations of off-the-shelf applications and fosters innovation.
Threat Watch
Proactive Threat Mitigation
Organizations can utilize Threat Watch to proactively identify and mitigate potential threats before they escalate into significant incidents. By employing its comprehensive analysis capabilities, businesses can enhance their security posture.
Compliance and Regulatory Adherence
Threat Watch helps organizations meet compliance and regulatory requirements by providing detailed insights into their cybersecurity health. This ensures that businesses remain aligned with industry standards and avoid potential penalties.
Incident Response Preparation
By leveraging the real-time insights and automated risk assessments of Threat Watch, organizations can better prepare for incident response. This feature ensures that teams are equipped with the necessary information to respond effectively to security breaches.
Employee Awareness and Training
Threat Watch can be used to educate employees about potential threats such as phishing addresses and compromised accounts. By raising awareness, organizations can foster a security-conscious culture and reduce the likelihood of human error leading to security breaches.
Overview
About Karolium
Karolium is a groundbreaking zero-code platform that revolutionizes the way businesses develop and customize applications. Designed for organizations seeking agility and efficiency, Karolium empowers users to rapidly create intelligent business solutions without requiring traditional coding skills. This platform is particularly advantageous for enterprises aiming to leverage artificial intelligence (AI) to enhance decision-making processes and streamline operations. Karolium features ready-to-deploy modules and a composability framework that allows seamless integration into existing application ecosystems. By offering built-in predictive and prescriptive analytics, it enables organizations to foresee trends and recommend optimal actions. With Karolium, businesses can accelerate their digital transformation journeys, responding swiftly to market demands and gaining a significant competitive edge.
About Threat Watch
Threat Watch is a state-of-the-art cybersecurity intelligence solution tailored to empower organizations with critical insights into their cyber health. It systematically analyzes an organization's assets, vulnerabilities, and exposures, providing a thorough overview of security status. Designed for businesses of all sizes, Threat Watch integrates real-time insights with automated assessments, allowing for the swift identification, prioritization, and mitigation of risks. By evaluating crucial security categories such as compromised credentials, breached accounts, phishing addresses, and dark web content, it equips users with essential information to take proactive measures against potential threats. The main value proposition lies in its ability to streamline the cybersecurity process, enabling organizations to respond more effectively to incidents and safeguard their digital assets. With Threat Watch, organizations can uncover their cybersecurity health quickly, ensuring they remain ahead of evolving threats.
Frequently Asked Questions
Karolium FAQ
What is zero-code development, and how does it benefit businesses?
Zero-code development allows users to create applications without the need for programming skills, making it accessible to non-technical staff. This accelerates the development process and empowers teams to innovate quickly.
How does Karolium integrate with existing systems?
Karolium is designed for seamless integration with both legacy systems and modern applications. Its flexible architecture allows organizations to connect new solutions without the complexities typically associated with traditional integration methods.
What types of analytics does Karolium provide?
Karolium includes built-in predictive and prescriptive analytics, enabling organizations to anticipate trends and receive actionable recommendations. This feature enhances decision-making and strategic planning.
Can Karolium support large enterprises?
Yes, Karolium is built as an enterprise-grade platform that supports unlimited users and extensive customization. Its robust capabilities make it suitable for businesses of all sizes looking to enhance their operations through intelligent applications.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for businesses of all sizes, from small startups to large enterprises. Its comprehensive features make it suitable for any organization looking to enhance its cybersecurity posture.
How does Threat Watch identify compromised credentials?
Threat Watch utilizes advanced scanning techniques to monitor various databases and dark web sources for compromised credentials associated with an organization's assets. This proactive monitoring helps organizations take immediate action.
Can Threat Watch integrate with existing security systems?
Yes, Threat Watch is designed to integrate seamlessly with existing cybersecurity tools and systems, enhancing an organization's overall security framework without disrupting current operations.
Is there a trial period available for Threat Watch?
Yes, Threat Watch offers a free scan for organizations to assess their cybersecurity health. This trial allows potential users to experience the solution's capabilities before committing to a subscription.
Alternatives
Karolium Alternatives
Karolium is a zero-code platform that facilitates digital transformation by enabling businesses to create and customize applications without the need for traditional coding skills. This innovative platform is designed for organizations aiming for agility and efficiency in their operations, harnessing AI-driven solutions to optimize decision-making and enhance productivity. As companies explore their options, many users seek alternatives to Karolium due to factors such as pricing, specific feature requirements, or compatibility with existing systems. When choosing an alternative to Karolium, it is essential to consider the platform’s ease of use, the level of customization offered, and the availability of robust analytics tools. Businesses should also evaluate the integration capabilities with their current software infrastructure and ensure that the alternative can support their long-term digital transformation goals. Ultimately, the right choice will depend on the unique needs and strategic objectives of the organization.
Threat Watch Alternatives
Threat Watch is a state-of-the-art cybersecurity intelligence solution designed to provide organizations with vital insights into their cybersecurity health. It falls under the business intelligence category, focusing on the assessment and management of security risks. Users often seek alternatives to Threat Watch for various reasons, including pricing concerns, feature sets that may better align with specific needs, or compatibility with existing platforms. When choosing an alternative, it’s essential to consider factors such as the comprehensiveness of security evaluations, the availability of real-time insights, and the effectiveness of automated assessments. The alternatives you explore should offer robust capabilities, particularly in monitoring compromised accounts and devices, as well as providing dark web insights. It's crucial to ensure that any replacement solution can deliver the same level of security assurance and operational efficiency that Threat Watch offers, thus enabling your organization to maintain a proactive stance against evolving cyber threats.