CMMC ROI vs Threat Watch
Side-by-side comparison to help you choose the right tool.
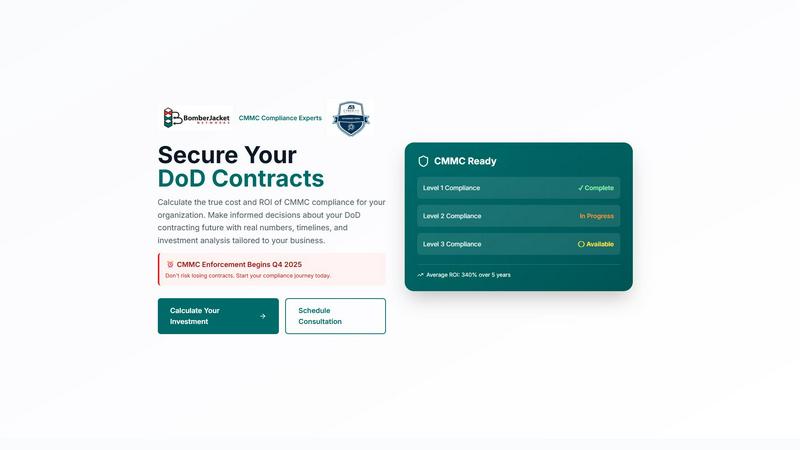
CMMC ROI
Measure your CMMC compliance ROI to confidently secure DoD contracts with tailored investment insights.
Last updated: March 1, 2026
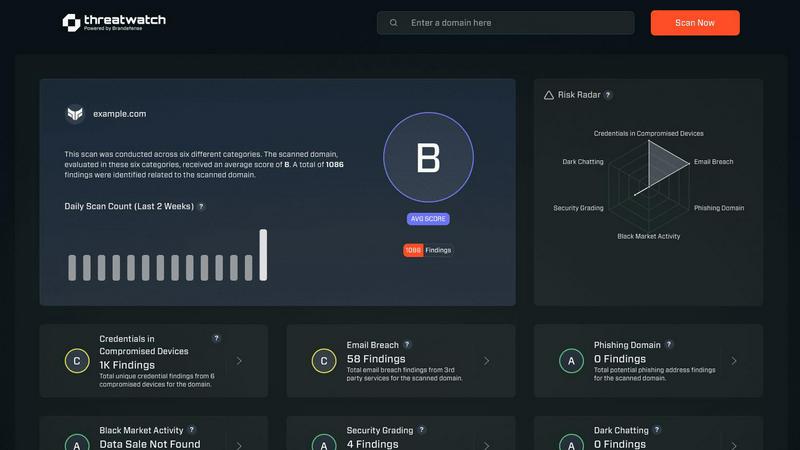
Threat Watch
Secure your digital world with Threat Watch, instantly revealing compromised accounts and devices for essential.
Last updated: March 1, 2026
Visual Comparison
CMMC ROI
Threat Watch
Feature Comparison
CMMC ROI
Personalized ROI Forecasting
CMMC ROI allows users to input specific company data, including size, revenue, and required CMMC level, to generate a tailored 5-year ROI forecast. This personalized analysis helps businesses understand the financial impact of their compliance efforts.
Comprehensive Investment Breakdown
The tool provides a detailed breakdown of implementation costs, including initial expenses, annual maintenance, and recertification fees. This comprehensive insight ensures that organizations can budget effectively and plan for future investments.
Risk Assessment Metrics
CMMC ROI includes critical risk assessment metrics that highlight the potential financial losses associated with non-compliance. By quantifying the risks, contractors can better appreciate the value of investing in CMMC certification.
Implementation Timeline Guidance
The tool outlines a clear timeline for achieving CMMC certification, detailing each phase—from gap assessments to final certification. This structured approach helps organizations stay on track and ensures all necessary steps are completed efficiently.
Threat Watch
Comprehensive Asset Analysis
Threat Watch provides an in-depth analysis of all organizational assets, identifying potential vulnerabilities and exposures that could be exploited by cybercriminals. This feature ensures that businesses have a clear understanding of their security landscape.
Real-Time Threat Insights
With real-time insights, Threat Watch keeps organizations informed about emerging threats and vulnerabilities. This timely information allows businesses to act swiftly and effectively, minimizing the potential impact of cyber incidents.
Automated Risk Assessment
The automated risk assessment feature streamlines the evaluation of security threats, saving time and resources. By automatically identifying and prioritizing risks, organizations can focus on the most critical issues, enhancing their overall security strategy.
Dark Web Monitoring
Threat Watch includes dark web monitoring to detect compromised credentials and sensitive information that may be available for sale. This proactive feature enables organizations to take immediate action to protect their data and reduce the risk of identity theft and fraud.
Use Cases
CMMC ROI
Small Contractor Compliance Planning
A small DoD contractor can utilize CMMC ROI to assess the financial implications of achieving Level 2 compliance. By entering their revenue and company size, they can understand their investment needs and the expected ROI over five years.
Large Contractor Risk Management
A large contractor with extensive DoD contracts can leverage CMMC ROI to analyze potential financial losses from non-compliance. This assessment allows them to make informed decisions about their cybersecurity investments and protect their revenue streams.
Strategic Bidding Enhancements
A technology firm aiming to bid on new DoD contracts can use CMMC ROI to evaluate the costs associated with compliance. This data-driven approach enables them to present competitive bids that reflect their commitment to cybersecurity.
Budget Allocation for Compliance
A medium-sized contractor can employ CMMC ROI to calculate the total investment required for CMMC compliance, including implementation and maintenance costs. This enables effective budget allocation and financial planning for compliance efforts.
Threat Watch
Proactive Threat Mitigation
Organizations can utilize Threat Watch to proactively identify and mitigate potential threats before they escalate into significant incidents. By employing its comprehensive analysis capabilities, businesses can enhance their security posture.
Compliance and Regulatory Adherence
Threat Watch helps organizations meet compliance and regulatory requirements by providing detailed insights into their cybersecurity health. This ensures that businesses remain aligned with industry standards and avoid potential penalties.
Incident Response Preparation
By leveraging the real-time insights and automated risk assessments of Threat Watch, organizations can better prepare for incident response. This feature ensures that teams are equipped with the necessary information to respond effectively to security breaches.
Employee Awareness and Training
Threat Watch can be used to educate employees about potential threats such as phishing addresses and compromised accounts. By raising awareness, organizations can foster a security-conscious culture and reduce the likelihood of human error leading to security breaches.
Overview
About CMMC ROI
CMMC ROI is a vital, data-driven investment calculator and strategic planning tool tailored specifically for contractors working with the Department of Defense (DoD). Its primary mission is to clarify the financial implications of achieving Cybersecurity Maturity Model Certification (CMMC) compliance. By translating complex security requirements into straightforward financial projections, CMMC ROI empowers businesses to make informed decisions regarding their investments in compliance. This tool is indispensable for any organization seeking, currently holding, or bidding on DoD contracts, as it offers a definitive analysis of the true costs associated with compliance versus the substantial returns on investment. By entering specific company metrics—such as size, DoD revenue, and target CMMC level—contractors receive a personalized 5-year ROI forecast, an estimated payback period, and a comprehensive overview of implementation expenses. With CMMC enforcement set to commence in Q4 2025, utilizing CMMC ROI is essential for protecting existing contract revenue, mitigating the risk of costly breaches, and securing a competitive edge in the defense industrial base. This tool transforms compliance from a perceived financial burden into a verifiable, ROI-positive necessity for sustainable business growth.
About Threat Watch
Threat Watch is a state-of-the-art cybersecurity intelligence solution tailored to empower organizations with critical insights into their cyber health. It systematically analyzes an organization's assets, vulnerabilities, and exposures, providing a thorough overview of security status. Designed for businesses of all sizes, Threat Watch integrates real-time insights with automated assessments, allowing for the swift identification, prioritization, and mitigation of risks. By evaluating crucial security categories such as compromised credentials, breached accounts, phishing addresses, and dark web content, it equips users with essential information to take proactive measures against potential threats. The main value proposition lies in its ability to streamline the cybersecurity process, enabling organizations to respond more effectively to incidents and safeguard their digital assets. With Threat Watch, organizations can uncover their cybersecurity health quickly, ensuring they remain ahead of evolving threats.
Frequently Asked Questions
CMMC ROI FAQ
What is CMMC ROI?
CMMC ROI is an investment calculator designed for DoD contractors to assess the financial implications of achieving Cybersecurity Maturity Model Certification (CMMC) compliance, providing personalized ROI forecasts and cost breakdowns.
How does CMMC ROI calculate ROI?
The ROI is calculated using the formula: ROI = (Protected Value - Investment) / Investment × 100. This takes into account the potential revenue from DoD contracts and the costs associated with compliance.
Why is CMMC compliance important?
CMMC compliance is crucial for DoD contractors as it not only ensures adherence to cybersecurity standards but also protects against financial losses from breaches and enhances competitive advantage in the defense contracting space.
When does CMMC enforcement begin?
CMMC enforcement is set to begin in Q4 2025. Contractors must take proactive steps towards compliance to secure their contracts and mitigate risks associated with non-compliance.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for businesses of all sizes, from small startups to large enterprises. Its comprehensive features make it suitable for any organization looking to enhance its cybersecurity posture.
How does Threat Watch identify compromised credentials?
Threat Watch utilizes advanced scanning techniques to monitor various databases and dark web sources for compromised credentials associated with an organization's assets. This proactive monitoring helps organizations take immediate action.
Can Threat Watch integrate with existing security systems?
Yes, Threat Watch is designed to integrate seamlessly with existing cybersecurity tools and systems, enhancing an organization's overall security framework without disrupting current operations.
Is there a trial period available for Threat Watch?
Yes, Threat Watch offers a free scan for organizations to assess their cybersecurity health. This trial allows potential users to experience the solution's capabilities before committing to a subscription.
Alternatives
CMMC ROI Alternatives
CMMC ROI is an essential financial tool categorized under business intelligence, specifically designed for contractors in the Department of Defense (DoD) sector. It aids users in calculating the return on investment associated with achieving Cybersecurity Maturity Model Certification (CMMC) compliance. As businesses increasingly seek to secure DoD contracts, many users look for alternatives due to factors like pricing, specific feature sets, or platform compatibility that may not meet their unique needs. When searching for an alternative, it's crucial to consider the tool's ability to provide personalized financial analysis, the comprehensiveness of its investment forecasting, and its alignment with your specific compliance requirements. The chosen solution should not only address your immediate financial concerns but also empower you with strategic insights that support long-term planning and decision-making in the competitive defense contracting landscape.
Threat Watch Alternatives
Threat Watch is a state-of-the-art cybersecurity intelligence solution designed to provide organizations with vital insights into their cybersecurity health. It falls under the business intelligence category, focusing on the assessment and management of security risks. Users often seek alternatives to Threat Watch for various reasons, including pricing concerns, feature sets that may better align with specific needs, or compatibility with existing platforms. When choosing an alternative, it’s essential to consider factors such as the comprehensiveness of security evaluations, the availability of real-time insights, and the effectiveness of automated assessments. The alternatives you explore should offer robust capabilities, particularly in monitoring compromised accounts and devices, as well as providing dark web insights. It's crucial to ensure that any replacement solution can deliver the same level of security assurance and operational efficiency that Threat Watch offers, thus enabling your organization to maintain a proactive stance against evolving cyber threats.
