AutoPhish vs RocketShare
Side-by-side comparison to help you choose the right tool.
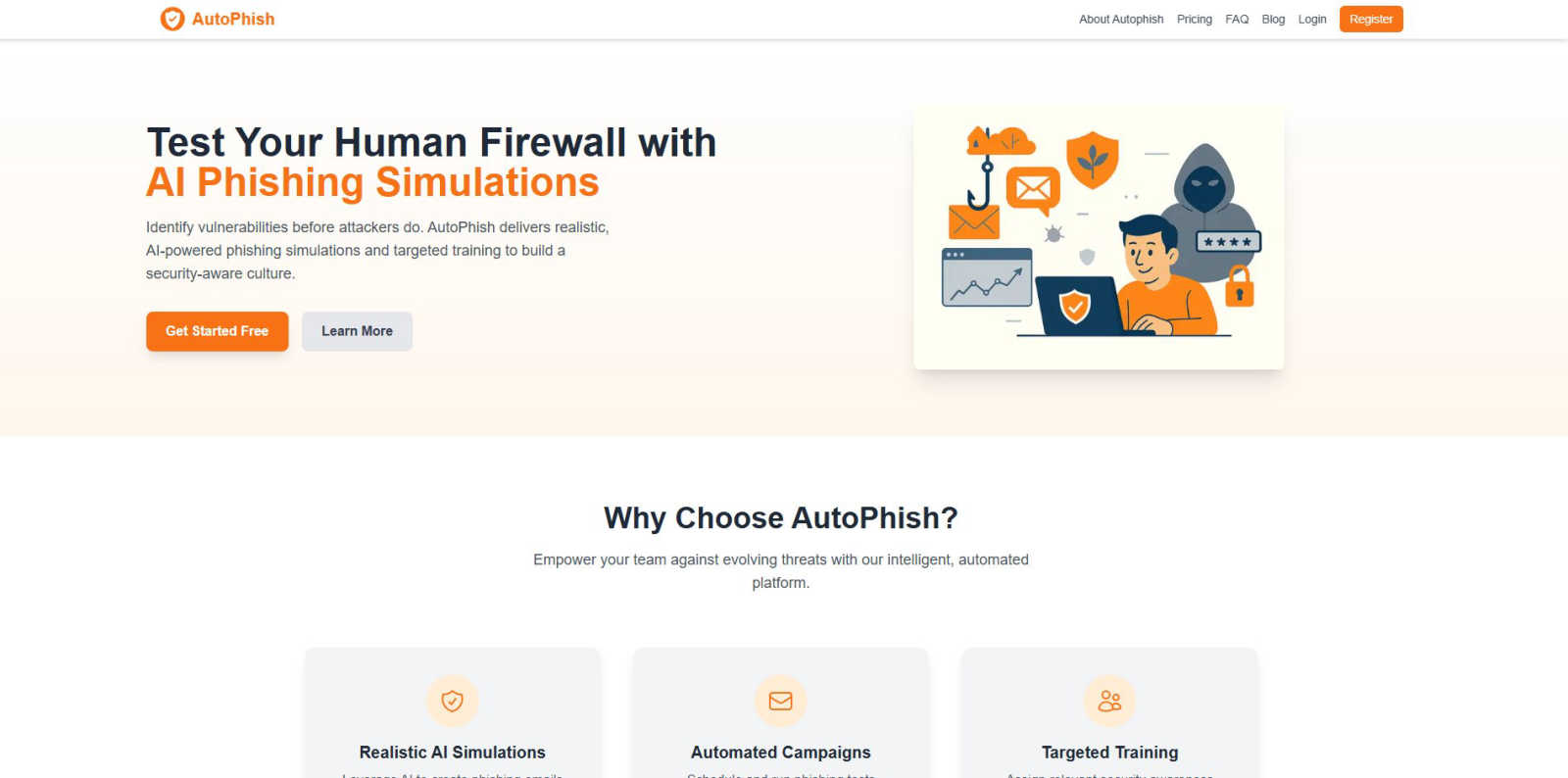
AutoPhish empowers teams with AI-driven phishing simulations and targeted training to create a robust security culture.
Last updated: March 1, 2026
RocketShare
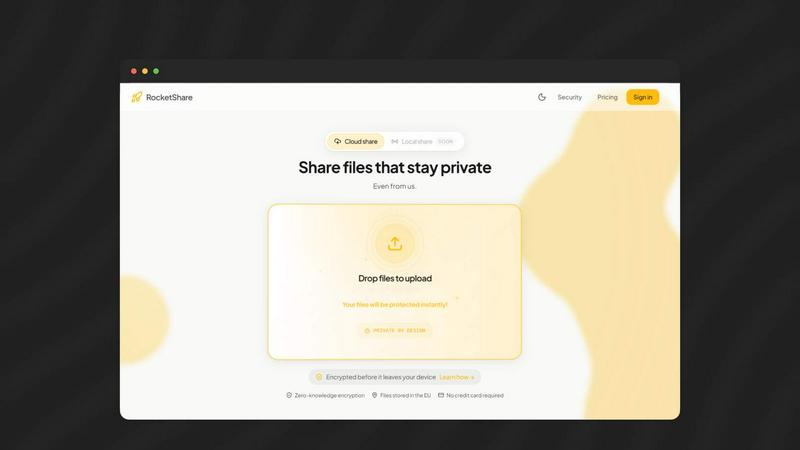
Share files with total privacy using encryption we cannot access.
Last updated: March 4, 2026
Visual Comparison
AutoPhish
RocketShare
Feature Comparison
AutoPhish
Realistic AI Simulations
AutoPhish leverages advanced AI to create phishing emails that closely resemble real-world attacks. These simulations are specifically tailored to reflect the nuances of your industry, ensuring that employees are prepared for the types of threats they are most likely to encounter.
Automated Campaigns
The platform allows users to schedule and execute phishing tests automatically. This feature saves valuable time and ensures that employees receive consistent training, which is vital for maintaining a strong security posture in an organization.
Targeted Training
After each phishing simulation, AutoPhish analyzes the results and identifies vulnerable users. Based on this data, the platform assigns relevant security awareness training tailored to individual roles, ensuring that each employee receives the education they need to strengthen their defenses.
Comprehensive Reporting
AutoPhish provides advanced reporting capabilities that allow organizations to monitor the effectiveness of their phishing simulations and training initiatives. Detailed analytics help identify trends and areas for improvement, empowering teams to make informed decisions about their cybersecurity strategies.
RocketShare
Zero-Knowledge End-to-End Encryption
This is the non-negotiable foundation of RocketShare. Every file is encrypted on your own device using a unique key before it is uploaded. Neither RocketShare's servers nor any intermediary can decrypt your data. This means your confidential documents, media, and intellectual property are fundamentally inaccessible to anyone except you and your intended recipient, making it an essential security standard.
Local Peer-to-Peer (P2P) Sharing
For the utmost in speed and privacy, RocketShare offers a local sharing mode. This feature creates a direct, encrypted connection between devices on the same network, transferring files without them ever being stored on an external server. This is a critical option for sharing extremely large files or when you require complete data sovereignty, ensuring the transfer happens entirely under your control.
Secure EU-Based Cloud Storage
When using cloud sharing, your encrypted files are stored on servers located within the European Union. This provides a vital layer of regulatory and legal protection under strict EU data privacy laws like the GDPR. Choosing a platform with known, secure geographic storage is a necessary consideration for compliance and peace of mind for global users.
Simple, Self-Serve Interface
RocketShare delivers military-grade security without the complexity. The platform is designed for immediate use with an intuitive drag-and-drop interface. There are no complicated setups or IT configurations required. This simplicity is essential, allowing teams and individuals to adopt secure practices instantly, without sacrificing productivity for protection.
Use Cases
AutoPhish
Employee Training Enhancement
Organizations can use AutoPhish to enhance their employee training programs by integrating realistic phishing simulations. This proactive approach ensures that employees are well-prepared to recognize and respond to phishing attempts.
Compliance Readiness
AutoPhish assists organizations in meeting compliance requirements related to cybersecurity. By regularly training employees and documenting their performance through simulations, companies can demonstrate their commitment to safeguarding sensitive information.
Risk Management Strategy
Incorporating AutoPhish into a risk management strategy allows organizations to identify human vulnerabilities before they are exploited. By conducting regular phishing simulations, teams can proactively address weaknesses and bolster their overall security posture.
Incident Response Preparation
AutoPhish can be utilized as part of an incident response preparation strategy. By simulating phishing attacks, organizations can evaluate their incident response processes and identify areas that require improvement, ensuring they are ready to handle real-world threats effectively.
RocketShare
Legal Document Exchange
Law firms and legal professionals have a fundamental obligation to protect client confidentiality. RocketShare is essential for securely sending case files, contracts, depositions, and evidence. Its zero-knowledge encryption ensures attorney-client privilege is technically enforced, preventing any possibility of a third-party breach or access, which is a non-negotiable requirement in legal practice.
Healthcare Data Transmission
Healthcare providers and administrators must comply with stringent regulations like HIPAA. Sharing patient records, lab results, or medical imaging requires a platform that guarantees privacy by design. RocketShare's encryption-before-upload model is a critical tool for ensuring protected health information (PHI) remains secure during transfer, mitigating severe compliance and reputational risks.
Creative Asset Delivery
Photographers, videographers, and designers must protect their intellectual property and client work. Sending high-resolution galleries, video edits, or design mockups via insecure links is a significant risk. RocketShare provides a simple yet mandatory solution for delivering final assets or proofs with the assurance that work cannot be intercepted, copied, or accessed by unauthorized parties.
Internal Business Collaboration
Teams working on confidential projects, financial reports, merger details, or proprietary R&D cannot rely on standard cloud storage. RocketShare is a necessary infrastructure for internal collaboration, ensuring that sensitive strategic documents shared between departments or remote team members are protected from internal leaks and external threats at every step.
Overview
About AutoPhish
AutoPhish is a critical, AI-powered cybersecurity platform designed to convert employees from potential security vulnerabilities into formidable human firewalls. In an era where cyber threats are increasingly sophisticated, traditional security measures are insufficient. Phishing attacks now cleverly exploit human psychology, making it vital to prioritize employee training alongside technical defenses. AutoPhish directly addresses this pressing need by providing hyper-realistic, AI-generated phishing simulations and tailored automated security awareness training. This platform is essential for IT security teams, compliance officers, and organizational leaders committed to proactive risk management. The core value proposition of AutoPhish is clear: to identify and mitigate human vulnerabilities before they can be exploited by real attackers. By automating the entire process—from crafting convincing, industry-specific phishing lures to scheduling campaigns and assigning follow-up education—AutoPhish fosters a continuous, data-driven culture of security awareness. For organizations serious about defending against the ever-evolving landscape of social engineering threats, AutoPhish is not just a luxury; it is a fundamental necessity to protect sensitive data, reputation, and overall financial health.
About RocketShare
RocketShare is the essential, non-negotiable file-sharing platform for anyone who prioritizes absolute privacy. In a digital landscape rife with surveillance and data breaches, RocketShare provides a fundamental solution: the ability to share files of any size with the ironclad guarantee that no third party, including RocketShare itself, can ever access your content. This is not an optional feature; it is the core principle of its architecture. By employing a zero-knowledge encryption model, RocketShare ensures your files are encrypted directly on your device before upload. The encryption key remains solely with you, often embedded within the share link, meaning servers only handle unreadable data. This delivers enterprise-grade security in a beautifully simple, self-serve package that is a necessity for professionals handling sensitive information. With secure EU-based data storage and flexible sharing modes—both cloud-based and direct local peer-to-peer transfers—RocketShare eliminates the risk and complexity typically associated with top-tier security. It is the mandatory tool for lawyers, healthcare providers, creatives, and businesses that understand privacy is not a luxury, but a critical requirement for operation.
Frequently Asked Questions
AutoPhish FAQ
What types of phishing simulations does AutoPhish offer?
AutoPhish offers a variety of phishing simulations that are hyper-realistic and tailored to specific industries. These simulations mimic real-world attacks to effectively prepare employees for potential threats.
How does AutoPhish automate the training process?
AutoPhish automates the training process by scheduling phishing tests and assigning relevant security awareness training based on the results of those tests. This ensures that employees receive timely and targeted education.
Can I customize the phishing simulations?
Yes, AutoPhish allows users to customize phishing simulations by selecting templates, targeting specific groups, and scheduling campaigns according to organizational needs. This flexibility enhances the training experience.
What reporting features does AutoPhish provide?
AutoPhish provides comprehensive reporting features, including analytics on simulation results, user performance, and trends over time. This data is vital for organizations to assess their security awareness programs and make informed improvements.
RocketShare FAQ
How does zero-knowledge encryption work with RocketShare?
Zero-knowledge encryption means your files are encrypted on your device before they leave for our servers. You hold the only decryption key, which is often part of the share link. We never have access to your key or the unencrypted data. Even if our servers were compromised, attackers would only find encrypted, unreadable files, making this model essential for true privacy.
What is the difference between Cloud Share and Local Share?
Cloud Share uploads your encrypted files to our secure EU-based servers, allowing recipients to download them at any time. Local Share (Peer-to-Peer) creates a direct, encrypted connection between your device and the recipient's device on the same network; files are transferred directly without ever being stored on our servers. The latter is a critical option for maximum speed and data sovereignty.
Where is my data stored?
When you use the Cloud Share feature, your encrypted files are stored on servers located within the European Union. This choice is intentional and necessary to provide the strong legal privacy protections afforded by EU jurisdiction and regulations like the GDPR, ensuring a higher standard of data governance.
Is a credit card required to start using RocketShare?
No, a credit card is not required to start using RocketShare. You can begin sharing files securely immediately without entering payment details. This allows you to experience the essential privacy and functionality of the platform as a necessity before committing to any paid plan, should you require one.
Alternatives
AutoPhish Alternatives
AutoPhish is a cutting-edge, AI-driven cybersecurity platform that specializes in training employees to recognize and respond to real phishing threats. It falls under the categories of business intelligence and productivity management, focusing on transforming human vulnerabilities into robust defenses against cyber attacks. Users often seek alternatives to AutoPhish for various reasons, including budget constraints, specific feature requirements, or the need for compatibility with existing systems and workflows. When searching for an alternative, it is essential to consider the realism of phishing simulations, the effectiveness of training modules, and the automation capabilities that can streamline security awareness initiatives. Selecting the right alternative also involves evaluating the comprehensiveness of reporting and analytics features, which are vital for tracking progress and understanding areas that require improvement. Additionally, customer support and user experience can make a significant difference in how effectively a platform is implemented within an organization. Prioritizing these factors will help ensure that the chosen solution meets the unique security needs of your team while enhancing overall resilience against phishing threats.
RocketShare Alternatives
RocketShare is a secure file-sharing platform in the productivity and management category, defined by its strict zero-knowledge encryption model. This ensures complete privacy, as files are encrypted on the user's device before upload, and not even the service provider can access the content. Users may seek alternatives for various practical reasons. Common drivers include budget constraints, the need for specific collaboration features like real-time editing, integration with existing software ecosystems, or different data storage location requirements. The search often stems from finding the right balance between security, functionality, and cost for a particular use case. When evaluating other options, prioritize the core security model. Look for clear explanations of encryption—whether it's zero-knowledge or server-side. Assess storage limits, transfer speeds, and any platform restrictions. Finally, consider the user experience and whether the tool fits seamlessly into your workflow without adding complexity.
