Hush Touch | Voice-to-Text for MacOS vs RedVeil
Side-by-side comparison to help you choose the right tool.
Hush Touch | Voice-to-Text for MacOS
Hush Touch offers seamless offline voice-to-text dictation for Mac, learning your vocabulary for precise, efficient.
Last updated: February 28, 2026
RedVeil
RedVeil delivers on-demand AI penetration testing to uncover real vulnerabilities fast.
Last updated: February 28, 2026
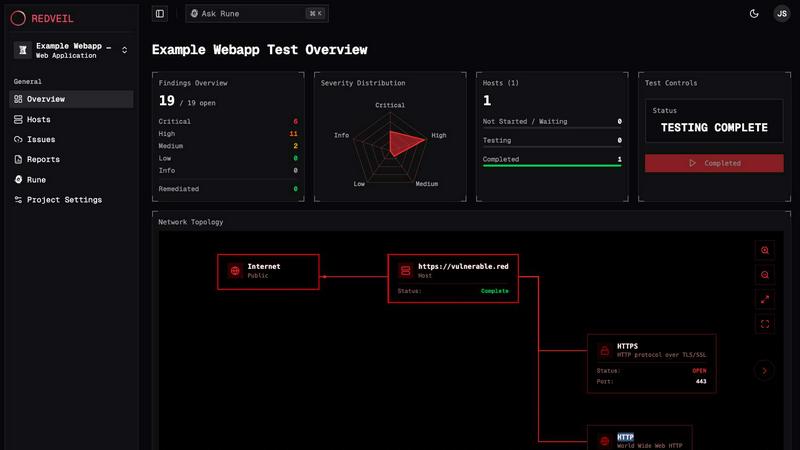
Visual Comparison
Hush Touch | Voice-to-Text for MacOS

RedVeil
Feature Comparison
Hush Touch | Voice-to-Text for MacOS
Dual-Engine Recognition
Hush Touch utilizes two sophisticated Apple dictation engines to provide an unparalleled dictation experience. The DictationTranscriber engine captures natural flow and punctuation, while the SFSpeechRecognizer enhances custom vocabulary recognition. This powerful combination ensures that your spoken words are transcribed accurately, making it ideal for professional environments where precision is crucial.
Custom Vocabulary
With the ability to store up to 500 custom terms, Hush Touch adapts to your unique language needs. It learns from your corrections and recognizes specialized jargon, brand names, and technical terms, making it perfect for professionals in fields like medicine, technology, and law. This feature ensures that the app evolves with you, improving its accuracy over time.
Smart Text Processing
Hush Touch incorporates intelligent text processing capabilities, including filler word removal, auto-correction for common mistakes, and formatting options for lists and snippets. This ensures that your transcriptions are not only accurate but also polished and professional, saving you time in the editing process.
Context Modes & Hands-Free Operation
Switch between different context modes like General, Email, Code, and Notes to tailor the dictation experience to your needs. With hands-free operation available through Siri, you can initiate dictation simply by voice, allowing for a truly seamless and efficient workflow.
RedVeil
Autonomous AI Attack Agents
RedVeil deploys intelligent AI agents trained to reason and execute multi-step attack chains like a real human attacker. These agents do not just run simple scans; they analyze, adapt, and exploit vulnerabilities by chaining together techniques to uncover deep security flaws and privilege escalation paths, providing depth that matches manual testing but at automated speed.
On-Demand Testing & One-Click Retesting
Eliminate the scheduling delays and scoping calls of traditional pentests. Start a comprehensive test whenever you need it, in minutes. After remediation, the One-Click Retesting feature is a must-have for validating fixes immediately, allowing you to close the security loop rapidly and continuously ensure your environment is secure after every change.
Compliance-Ready Reporting
Generate professional, detailed reports with a single click, formatted and structured to meet the stringent requirements of major compliance frameworks. These reports are immediately suitable for SOC 2, ISO 27001, PCI-DSS, and other audits, providing executives, engineers, and auditors with clear evidence, context, and verified findings without requiring manual compilation.
Guided Remediation & AI Expert (RUNE)
Every finding includes clear reproduction steps, impact analysis, and specific remediation guidance. The integrated AI expert, RUNE, provides essential support by helping set test scope, explaining complex attack paths in plain language, and offering step-by-step fix guidance, ensuring your team can understand and resolve issues efficiently.
Use Cases
Hush Touch | Voice-to-Text for MacOS
Drafting Emails
Hush Touch is perfect for busy professionals who need to draft emails quickly and efficiently. Simply dictate your message, and the app will handle punctuation and formatting, allowing you to focus on your content rather than typing.
Taking Notes
Students and researchers can benefit immensely from Hush Touch by dictating lecture notes or ideas on the go. The app's ability to recognize specialized vocabulary makes it a valuable tool for capturing complex concepts accurately.
Document Creation
Whether you are writing reports, articles, or creative content, Hush Touch enables you to create documents hands-free. The adaptive learning feature allows it to learn your writing style, ensuring your documents maintain a consistent voice.
Coding and Technical Documentation
For software developers and engineers, Hush Touch offers a unique advantage by accurately recognizing technical terms and jargon. This helps streamline the creation of code comments and technical documentation, enhancing productivity.
RedVeil
Continuous Compliance Validation
For companies undergoing SOC 2, ISO 27001, or PCI-DSS audits, RedVeil is a necessity for providing continuous evidence of due diligence. Instead of relying on a single annual point-in-time test, you can run tests before major releases or quarterly audits, generating fresh, compliant reports on-demand to prove ongoing security commitment to auditors.
Pre-Deployment Security Gates
Integrate RedVeil into your CI/CD pipeline or run it manually before deploying new features or applications. This use case is critical for DevOps teams to identify and remediate exploitable vulnerabilities before they reach production, shifting security left and preventing costly post-launch fixes and potential breaches.
Proactive Attack Surface Management
Regularly test your external and internal network perimeter for new vulnerabilities as your attack surface evolves. RedVeil allows security teams to schedule or run tests frequently without budget or scheduling constraints, ensuring you discover misconfigurations and weaknesses that could be targeted by attackers.
Vendor and M&A Security Due Diligence
During mergers, acquisitions, or when onboarding new third-party vendors, conducting a rapid security assessment is essential. RedVeil enables you to perform a thorough, AI-driven penetration test on external assets quickly, providing a data-driven security snapshot to inform critical business decisions without lengthy delays.
Overview
About Hush Touch | Voice-to-Text for MacOS
Hush Touch is a cutting-edge voice-to-text application designed specifically for macOS users who seek a fast, natural, and private dictation experience. This essential tool operates entirely on-device, ensuring that your voice data remains secure and offline, eliminating the need for cloud dependency. With a lightweight footprint of just 5.5 MB, Hush Touch integrates seamlessly into your daily writing routines, allowing users to draft emails, messages, notes, documents, and more hands-free. By harnessing the power of dual Apple transcription engines and an advanced Apple Intelligence final processing pass, Hush Touch delivers remarkably accurate and polished text. Whether you are a professional or a casual user, this app enhances your productivity by learning your vocabulary over time, improving punctuation, and helping you maintain a clear tone while respecting your privacy. With a one-time purchase of just $20 for a lifetime license, Hush Touch is an indispensable tool for anyone looking to elevate their dictation experience on Mac.
About RedVeil
RedVeil is an essential AI-powered penetration testing platform built for the modern, fast-paced engineering environment. It fundamentally replaces the outdated, slow, and expensive model of traditional manual pentesting. Where traditional methods require scheduling consultants weeks in advance, cost tens of thousands for a single snapshot, and create security bottlenecks, RedVeil delivers the critical reasoning of a human hacker with the necessary speed and scalability of software. It is designed for security teams, DevOps engineers, and companies that deploy code frequently and cannot afford to wait for annual security audits. The core value proposition is non-negotiable: operationalize your security testing. You can spin up a full, autonomous penetration test in minutes and receive a detailed, actionable, and audit-ready report within hours, not weeks. This enables continuous security validation aligned with agile development cycles, ensuring vulnerabilities are identified and can be remediated at the speed of your business, making robust security a practical necessity rather than a logistical burden.
Frequently Asked Questions
Hush Touch | Voice-to-Text for MacOS FAQ
How does Hush Touch ensure privacy?
Hush Touch processes all voice data entirely on your Mac, with zero reliance on cloud services. This means your information remains secure and private, providing peace of mind as you dictate.
Can I customize the vocabulary?
Yes, Hush Touch allows you to store up to 500 custom terms and learns from your corrections, adapting to your specific vocabulary needs over time.
Is there a trial version available?
Absolutely! Hush Touch offers a 7-day free trial with no credit card required, allowing you to experience its features firsthand before making a purchase.
What happens if I need support or assistance?
Hush Touch provides comprehensive support resources, including FAQs and a user guide, ensuring you have all the assistance you need to make the most of the app.
RedVeil FAQ
Does RedVeil perform a real penetration test?
Yes. RedVeil is not a simple vulnerability scanner. It performs genuine penetration testing using autonomous AI agents that reason through multi-step attack chains, exploit vulnerabilities, and uncover complex security flaws just like a human ethical hacker, delivering verified, exploitable risks with evidence.
How many penetration tests can I do with my annual subscription?
Testing capacity is based on an "Agent Ops" effort model. For example, the Perimeter plan includes 500 Agent Ops annually, and the Full Coverage plan includes 2,500. You can allocate these ops to run multiple tests throughout the year, allowing for regular testing aligned with your development and compliance cycles.
Can I use RedVeil's reports for compliance audits?
Absolutely. A core feature of RedVeil is generating professional, audit-ready reports specifically structured to meet the requirements of major frameworks like SOC 2, ISO 27001, and PCI-DSS. The reports provide the detailed evidence, executive summaries, and technical findings that auditors require.
What if I have concerns about submitting my report to my auditor?
RedVeil's reports are designed to provide the necessary assurance. They include clear documentation of the testing methodology, scope, and verified findings with evidence. For additional support, the platform's AI expert (RUNE) can help explain findings and the process to provide further context to your auditor.
Alternatives
Hush Touch | Voice-to-Text for MacOS Alternatives
Hush Touch | Voice-to-Text for MacOS is a cutting-edge dictation app designed specifically for macOS users who prioritize privacy and efficiency. As part of the AI Assistants category, it offers a reliable and natural voice-to-text experience by leveraging advanced on-device technology. Users often seek alternatives to Hush Touch due to various reasons, including pricing, specific feature requirements, or compatibility with different platforms. When choosing an alternative, consider factors such as offline functionality, accuracy of transcription, ease of use, and the overall integration with your writing workflow. A good alternative should also provide a balance of privacy and performance while fitting within your budget and meeting your dictation needs.
RedVeil Alternatives
RedVeil is an AI-driven penetration testing platform that automates security assessments. It belongs to the category of AI-powered cybersecurity tools, designed to provide fast, on-demand vulnerability discovery and audit-ready reporting at a competitive price point. Users often explore alternatives for various reasons. These can include budget constraints, the need for specific integrations with their existing tech stack, or a preference for a different deployment model, such as a fully managed service versus a self-serve tool. Some teams may also seek solutions with a stronger focus on human-led testing or compliance with particular regulatory frameworks. When evaluating alternatives, key considerations should be the solution's speed and frequency of testing, the depth and accuracy of its findings, the flexibility of its scheduling and targeting, and the comprehensiveness of its reporting for compliance needs. The ideal tool should align with both your security requirements and your engineering team's agile workflow.
